Automated creation of a minimal AWS EC2 AMI with NAT support.
In the official NAT instance AMI provided by AWS, the root EBS volume is 8GB while the actual size of all files is well under 2GB. Using standard methods it is not possible to decrease size of an EBS volume while keeping the entire file-system intact.
The code is also quite generic and can be adjusted to help with different use-cases.
- Set up a user with access keys
- Make sure the user can assume admin [role]
- Make sure the role requires MFA device, for example Google Authenticator
In my case it looks similar to:
# cat ~/.aws/credentials
[auto_admin]
aws_access_key_id = XXX
aws_secret_access_key = XXX
# cat ~/.aws/config
[default]
region = eu-central-1
[profile auto_admin]
role_arn = arn:aws:iam::123456789012:role/admin_role_for_auto_admin
source_profile = auto_admin
mfa_serial = arn:aws:iam::123456789012:mfa/auto_adminIn the cloned directory of this repository:
# Make sure the top level variables look sensible
cat vars.yml
sed -i 's/123456789012/210987654321/' vars.yml
# Execute playbooks one by one
ansible-playbook sandbox_create_playbook.yml -e mfa_token=123456
ansible-playbook usecase_create_playbook.yml
ansible-playbook usecase_test_playbook.yml
ansible-playbook usecase_destroy_playbook.yml
ansible-playbook sandbox_destroy_playbook.yml -e mfa_token=123456- The code was created and tested on Linux Mint
- ansible 2.7.6
- aws-cli/1.16.96 Python/2.7.15rc1 Linux/4.18.0-13-generic botocore/1.12.86
- It exercises a somehow disputable trick of using an existing mini-ami and overriding entire file-system except the old Grub 0.97 in the boot-record
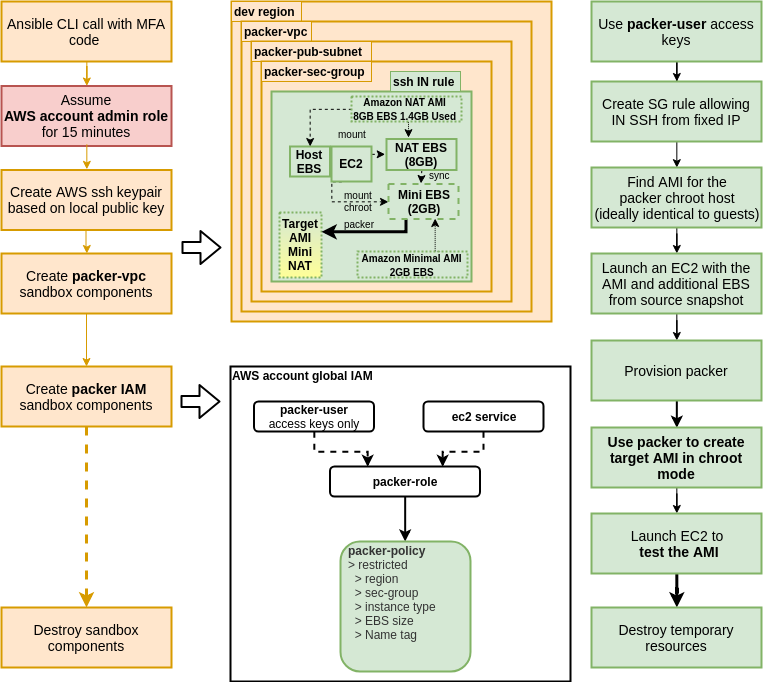
- Here is a diagram depicting the flow: