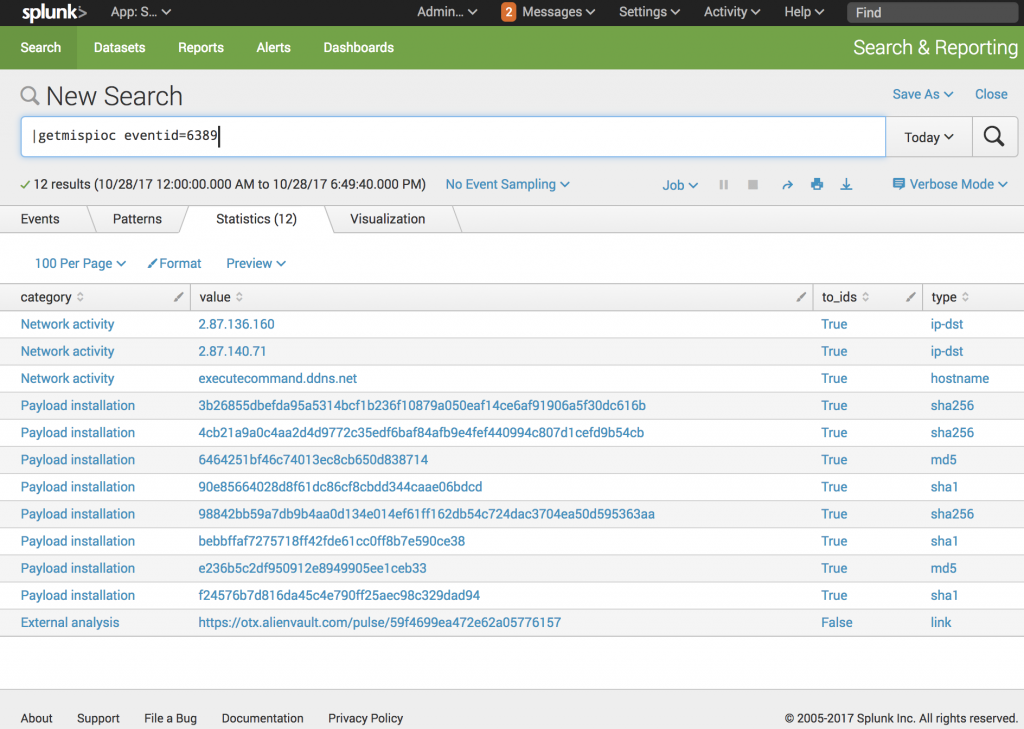
getiocmisp is a Splunk custom search command that helps to extract IOCs from a MISP instance.
getiocmisp relies on PyMISP. PyMISP requires Python 3 but only Python 2.7 is available in the Splunk environment. The script getiocmips.py is a wrapper and calls get-ioc-misp.py. This is best to keep your Splunk instance clean.
- Install Python 3 on the Splunk server
- Install Splunk-SDK for Python (see http://dev.splunk.com/view/python-sdk/SP-CAAAEDG)
- Install PyMISP (see https://github.com/CIRCL/PyMISP). Install it from Github
-
Copy app_getmispioc to $SPLUNK_HOME/etc/apps/
-
Copy scripts/* to /usr/local/bin/
-
Verify permissions. Files owned by splunk -user and .py files are executable
-
Edit /usr/local/bin/mispconfig.py and specify your MISP URL and authorization key
-
Restart Splunk
See https://blog.rootshell.be/2017/10/31/splunk-custom-search-command-searching-misp-iocs/