Would you volunteer your company for a cyber attack? While that concept may sound strange, that is exactly what businesses and government organizations utilize ZibaSec to do. In today’s increasingly digital world, cybersecurity is much more important now more than ever. Research has shown that 91% of all cyber attacks start with a phishing email. While there are many products and services that scan servers and code for vulnerabilities, ZibaSec enables organizations to simulate sophisticated phishing campaigns against their own workforce to scan for human vulnerabilities. The resulting data allows them to better defend their organization from actual phishing attacks.
With a small remote team of seven, ZibaSec has been able to build its complex software and is in the process of becoming FedRAMP certified, which allows cloud service providers to work with federal agencies and hold federal data. From a business standpoint, the FedRAMP certification opens the door for them to work with just about any agency in the federal government. “That was a huge accomplishment for us, especially as a start-up,” said Julie Davila, CEO and Co-founder. “There are hardly any start-ups in the federal space that are exclusively delivered as a service.”
Meeting FedRAMP regulations is a difficult task even for large companies. There are many rules and strict processes companies must adhere to. For example, the Change Control Board (CCB) is an integral part of the FedRAMP certification. It is typically made up of various stakeholders, such as an operations manager, application owner, security team, engineers, and whoever is requesting the change, which could be the customer. All the requested changes, including any possible effects on security or operations, must be documented, reviewed, and approved by the CCB before these changes can be pushed into production. This can be a slow-moving process, particularly for larger organizations with more stakeholders involved.

Despite being a small team, ZibaSec found ways to make the most of their workflow, like speeding up their CCB process by automating notifications and approval tracking through a repository powered by GitHub Actions. This system creates a standard template to be filled out, concatenates raw data into different files, then commits the files back into the repository. When a change needs to be made, a bash script creates Markdown templates in the required format. These can then be copied into a pull request message on GitHub for approval. “We’ve essentially modernized a historically ‘paper and three-ring binder’ process using a GitHub repository,” said Victoria Drake, Director of Engineering.
ZibaSec decided to use GitHub because “the other options were really bad,” stated Dan Shepherd, CTO and Co-founder of ZibaSec. They needed a tool that had version control to track and document every change. “It just made sense,” said Shepherd. “We were already using GitHub for other things. We now use GitHub Actions to work like a much larger team.”
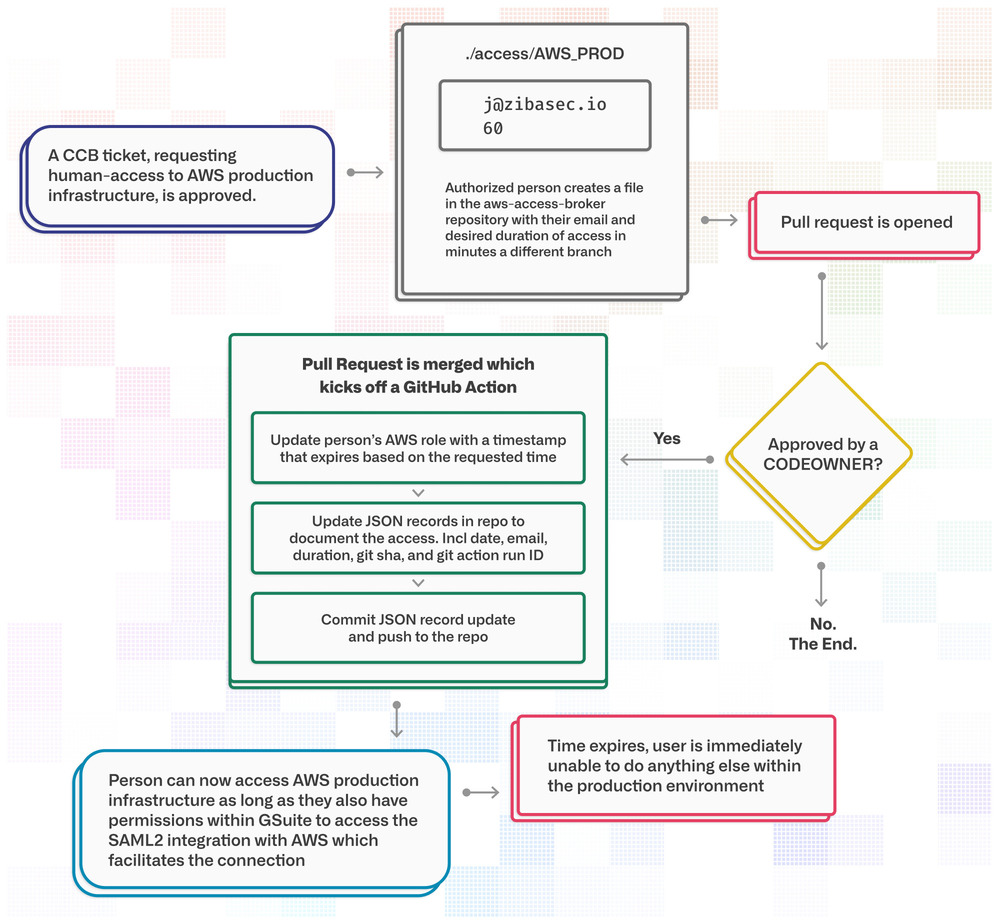
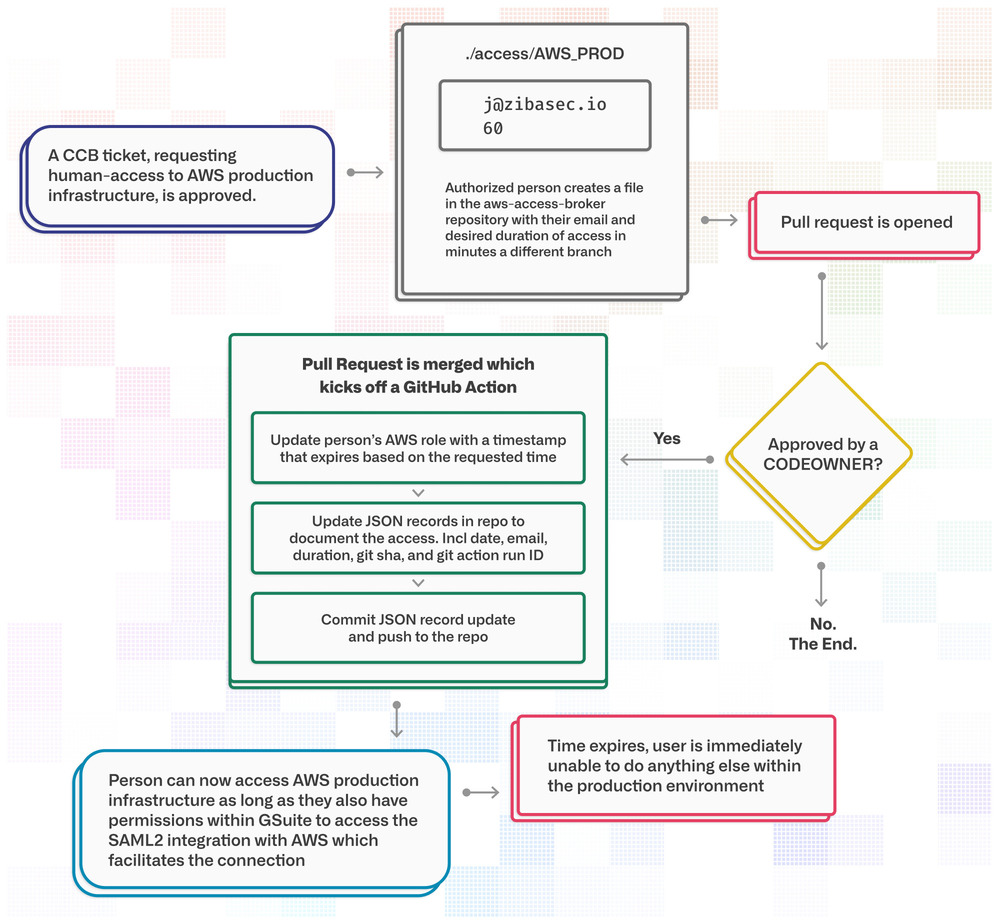
The ZibaSec team didn’t want to depend on any single person to control access to production. With a team of seven wearing many hats, a requested task could sit in a ticket backlog or half the team could be out of office at once. Instead, they created an automated system to broker access to AWS. Now, anyone on the team can request access through the “AWS Access Broker” repository. Once approved by someone through GitHub approvals, Actions grants temporary access for that person to the production account, accessed through G Suite’s SAML integration into AWS. This helped alleviate concerns that an enterprise organization might have about a young company like ZibaSec. “We do everything we can to minimize the amount of trust we place on people, and let technology grant access in a way that’s well-controlled, documented, and versioned,” said Davila.
“What I love about GitHub Actions is that you’re not limited in your choice of tools,” says Drake. GitHub’s library of pre-built actions makes it easy to integrate any tool to customize your technology ecosystem. ZibaSec currently uses Terraform and Serverless Framework through AWS combined with actions to enable automatic deploys. Changes go through multiple layers of approval including several branch protection rules in GitHub. Once everything is approved and merged, actions kick off and deploy the changes to production. Managing this through GitHub allows ZibaSec to maintain a thorough record of changes so they can meet the FedRAMP requirements without having to slow down.
It comes as no surprise that security is particularly important when working with federal agencies and their data. ZibaSec uses automation and GitHub’s security features to ensure that nothing slips past their attention. GitHub Advanced Security runs checks on every pull request and displays the results. They’ve also created a tool that piggybacks off Dependabot in order to facilitate their reporting needs. Using the GitHub API, the tool extracts vulnerability reports into a native interface so the team can clearly extract the artifacts they’d need for an audit.
If a vulnerability is detected, a GitHub issue is opened. FedRAMP requires that these issues be resolved and closed within a certain timeframe, depending on the severity of the issue. GitHub issues provide a detailed tracking mechanism for ZibaSec to show FedRAMP auditors when a vulnerability was detected, when it was addressed (when the issue was opened), when it was patched or discarded (when the issue was closed), or if it was a false positive.

FedRAMP requires a lot of documentation, and any vulnerability detected by any tool is considered a legitimate finding that needs to be addressed. Even if the vulnerability turns out to be a false positive, it would still need to be documented—time-consuming work that other static analysis tools haven’t helped the team avoid. Previously, ZibaSec had used other static analysis tools but found they generated unnecessary work due to false positives. “We haven’t run into any false positives with Advanced Security,” said Shepherd. “Accuracy is crucial because we don’t want to spend time writing documentation. We want to find tools that are going to help us rather than create more work.”
The team has saved even more time by going serverless with GitHub Enterprise Cloud. Because ZibaSec doesn’t run on its own data centers, physical servers, or machines, FedRAMP’s regulations regarding physical security don’t apply to them. ZibaSec does not have to bear the responsibility of managing and scanning server hosts. “With our team size, it’s highly unlikely that we would have been able to meet the federal requirements without a serverless model,” Davila stated. “But by entrusting that process to vendors like GitHub, we have saved so many hours and dollars.”
We haven’t run into any false positives with Advanced Security. Accuracy is crucial because we don’t want to spend time writing documentation. We want to find tools that are going to help us rather than create more work.
While security and documentation are a high priority for the team, they still value the importance of open source communities. In a world where transparency is almost non-existent, they feel it’s important to be as transparent as possible with end-users and organizations about their use of data. ZibaSec hosts a number of open source repositories and contributes to the community through issues as well as code contributions.

“I think it’s very valuable to practice learning and building in public,” said Drake. “Some organizations refrain from open source because there is some potential for security missteps, but the benefits far outweigh the risks. What people don’t realize is that you can simultaneously be secure and open sourced.” With GitHub being the “de facto standard” for open source communities, they can trust that it will provide a secure environment.
For ZibaSec, GitHub was more than just a traditional code repository. With the flexibility provided by actions and the GitHub API, they are able to function at the level of a more mature company and achieve more than would seem possible with a team of seven. “It’s a huge accomplishment for just seven people to have gotten as far with FedRAMP as we have,” said Drake. “GitHub is part of our story and deserves credit for our success.”